How Trojan Malware Infiltrates Your Devices and Steals Data
Have you ever downloaded a program that promised to boost the speed of your computer? However, as soon as you run it, nothing happens—or at least you think nothing happened. In this scenario, you might have just infected your PC with Trojan malware.
The name Trojan instills fear in those who are even mildly aware of malware. So what exactly is a Trojan, and how can you make sure your computer is safe from it? This article will go through everything you need to know about this sneaky adversary.
How Trojans Work and Their Disguises
The reason this malware is named after the Trojan horse is because it operates in the same way. It pretends to be harmless software to bypass your computer’s defenses. Unlike computer viruses, Trojans don’t self-replicate, but they can be just as destructive.
A Trojan is often disguised as something else to go unnoticed by the average user. It might be disguised as an installer or a software updater, except it will install other malware instead of the promised software. Moreover, a phishing email might contain a doc file with a macro programmed to install a Trojan.
Another way a Trojan can get into your system is when you browse unsafe or vulnerable websites. Drive-by downloads can happen just by clicking an ad on these sites or even by opening the website itself.
The infection process
Remember, the goal of a Trojan is to infiltrate a computer and create a backdoor. Through this backdoor, attackers can gain remote access and control the machine. Deploying Trojans often involves social engineering. Victims are often manipulated to disable their security features to make it easier for Trojans to infiltrate their systems and carry out malicious actions.
A Trojan’s Next Step: Data Theft and More
If someone has already installed a Trojan on your machine, the next step is usually data theft. Sensitive information like passwords and banking details stored in easily accessible folders is the target.
In some cases, the threat actor may not steal data straight away. They might hang around on your machine for a bit to see what you do. This gives them time to assess the situation and plan their data extraction.
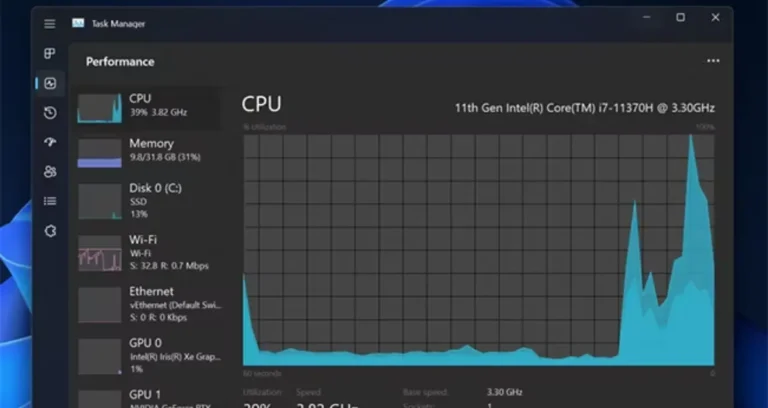
Beyond data theft, a Trojan can turn your machine into a botnet for malicious purposes, like a DDoS attack or mining cryptocurrency, slowing your computer down.
How to Dodge or Eliminate a Trojan
Now that you know how damaging a Trojan can be, it’s time to dive into steps to avoid getting infected by one.
Browse responsibly and be vigilant
When browsing the internet, be cautious of suspicious websites, verify sources, and be wary of emails that may contain malicious attachments or links.
Utilize the best anti-Trojan software
Several anti-virus and anti-malware software programs can detect and remove Trojans. Make sure to update them and scan your computer regularly, especially after you’ve downloaded new files.
Use a VPN to enhance your online security
While a Virtual Private Network doesn’t directly stop a Trojan from executing, it can help in different ways. Since your data traffic is encrypted, attackers can’t inject malicious code into the website you’re visiting because they cannot see it. Some VPN Providers also offer features like malware blocking and website filtering. Make sure to choose the best VPN for your needs.
Strengthen your account security with a password manager
If a Trojan is already on your computer, a password manager can mitigate the damage it can do by securing your credentials. Since autofill features don’t require keystrokes, any keylogger installed by the Trojan won’t be able to capture your password.
Also, even if one password is compromised, it can’t be reused since password managers make sure you have unique passwords for every account. Furthermore, if your master password is stored in a different device, hackers won’t be able to compromise your credentials stored in the password manager. Not to mention, they must still circumvent two-factor authentication.
Don’t Let That Horse In
A Trojan malware can wreak havoc, and it can be very sneaky. Fortunately, with safe online habits and the right security tools, it becomes less of a threat. Just follow the advice in this article, and you won’t end up like the people of Troy in the Greek story. Keep your digital walls secured!